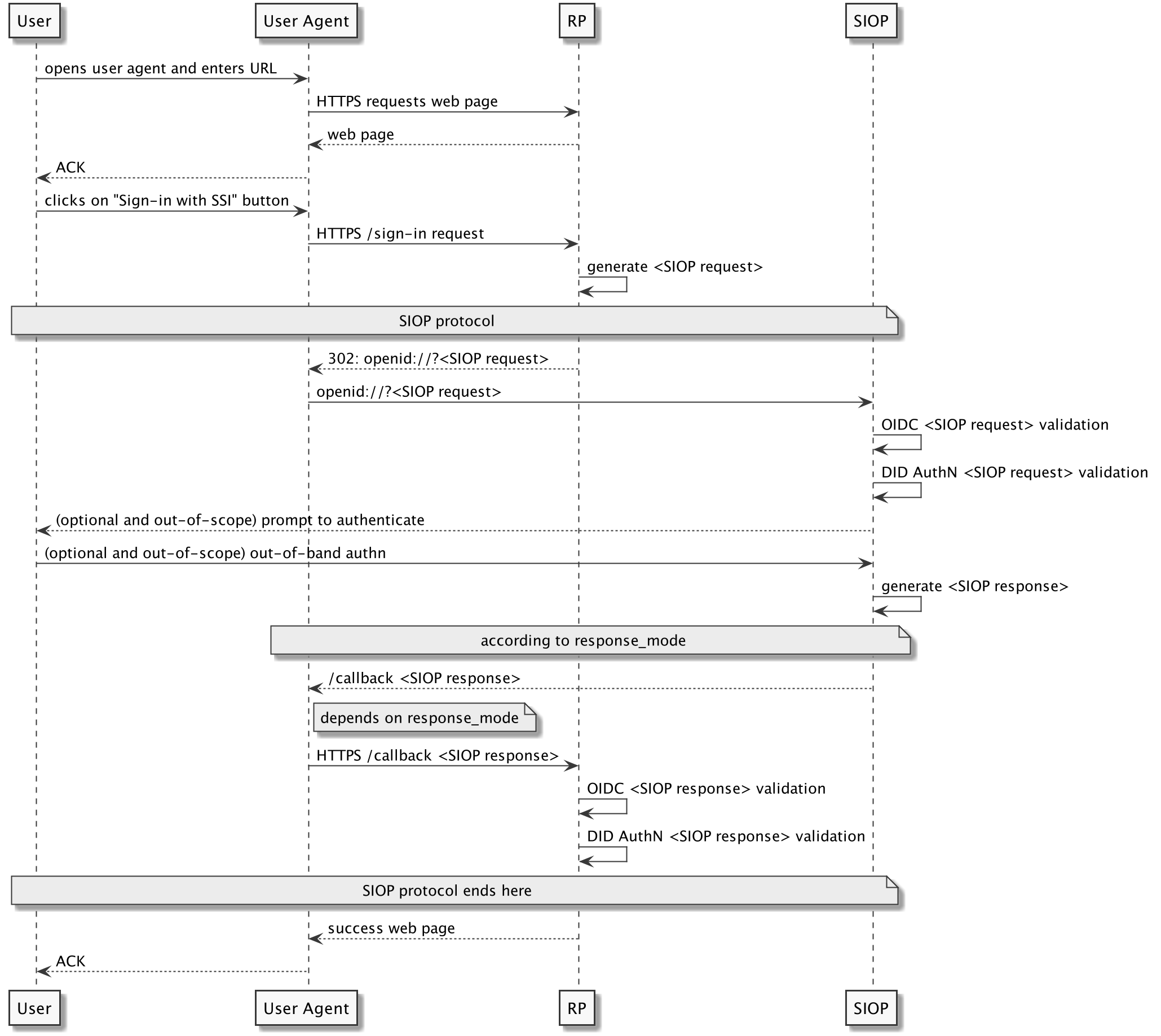
Protocol Flow
This specification assumes, the user is operating a mobile or desktop browser to visit a web application or uses a browser-based app.
First, the user clicks on the sign up or login UX element. The RP will then generate the
redirect to openid://<SIOP Request> which will be handled by the SIOP.
On the mobile device, this would open the Identity Wallet app, e.g., uport,
connect.me. On the desktop browser, this would either show a QR code which can be scanned by the
Identity Wallet app or a redirect to openid://<SIOP Request>
that for instance could be handled by a browser extension/ plugin implementing the SIOP.
The SIOP will generate the <SIOP Response> based on the specific
DID method that is supported. The <SIOP Response> will be signed and
optionally encrypted and will be provided according to the requested response mode.
This specification does not explicitly support any intermediate hubs or cloud agents. It is meant to be a protocol to exchange the DID. You could then interact with a hub/ cloud agent using the service endpoint in the DID Document.
Unlike the OIDC Authorization Code Flow as per [[!OIDC.Core]], the SIOP will not return an access token to the RP. If this is desired, this could be achieved by following the aforementioned CIBA flow as per [[?OIDC.CIBA]] in addition. SIOP also differs from Authorization Code Flow by not relying on a centralized and known OP. The SIOP can be unknown to the RP until the user starts to interact with the RP using its Identity Wallet. OIDC Authorization Code Flow is still a useful approach and should be used whenever the OP is known, and OP discovery is possible, e.g., exchanged or pre-populated DID Document containing an openid element in the service section. The SIOP flow allows to integrate Identity Wallets with plain OIDC clients if they implemented the SIOP specification. In contrast, using DID AuthN as the authentication means in the OIDC Authorization Code Flow would require integration with the OP vendor itself.
Generate SIOP Request
Redirect Request
The request contains scope, response_type and client_id as query
string parameters for backward compatibility with the OAuth2 specification [[!RFC6749]].
response_type MUST be id_token and client_id MUST specify the
redirect URI of the RP (as per [[!OIDC.Core]]). All other OIDC
request parameters MUST be provided in an Request Object as per [[!OIDC.Core]] which is encoded as a JWT.
This enables the RP to authenticate against the SIOP using the
RP's DID. The Request Object can be passed by value in the
request request parameter, or by reference using the request_uri parameter.
openid://?response_type=id_token
&client_id=https%3A%2F%2Frp.example.com%2Fcb
&scope=openid%20did_authn
&request=<JWT>
In the example above the DID AuthN <SIOP Request> is initiated
by the RP using Request Object by value.
openid://?response_type=id_token
&client_id=https%3A%2F%2Frp.example.com%2Fcb
&scope=openid%20did_authn
&request_uri=https%3A%2F%2Frp.example.com%2F90ce0b8a-a910-4dd0
In the example above the DID AuthN <SIOP Request> is initiated
by the RP using Request Object by reference.
RP Metadata
In contrast to other OIDC flows, e.g., Authorization Code Flow, RPs
can provide client metadata in the registration request parameter. Clients MAY include
any registration metadata parameters defined in OpenID Connect Registration 1.0, and servers MAY use these parameters as they see fit.
In addition to RS256, an SIOP according to this specification MUST support
EdDSA and ES256K [[!draft-ietf-cose-webauthn-algorithms-03]] for
request_object_signing_alg and request_object_signing_alg can be omitted.
RPs implementing the DID AuthN profile MUST not use
none for request_object_signing_alg.
The Request Object MUST be directly or indirectly verifiable by a verification method in the
RP's DID Document and directly by the RP's
JWKS. The JWKS MUST be provided in the jwks_uri or jwks entry of the
registration parameter. The JWKS MUST contain an entry with a kid that matches
the kid in the Request Object. jwks_uri MUST use the HTTP(S) DID Resolution
Binding as per [[DID.Resolution]] for backward compatibility reasons with plain SIOP
OPs. The jwks request parameter SHOULD be used only if the public key cannot
be directly obtained from the DID Document.
RPs can decide to receive the SIOP Response encrypted. To enable encryption,
the registration parameter MUST use id_token_encrypted_response_alg and
id_token_encrypted_response_enc according to OIDC Client Metadata
[[!OIDC.Registration]]. This specification RECOMMENDS the use of `ECDH-ES` with the `X25519` curve for JWE
as explained in section Encryption and described in
[[!draft-amringer-jose-chacha-00]].
Request Object
The Request Object follows the OIDC specification, e.g., adding nonce,
state, response_type, and client_id parameters.
The request contains scope, response_type and client_id as query
string parameters for backward compatibility with the OAuth2 specification [[!RFC6749]].
response_type MUST be id_token and client_id MUST specify the
redirect URI of the RP (as per [[!OIDC.Core]]). All other OIDC
request parameters MUST be provided in an Request Object as per [[!OIDC.Core]] which is encoded as a JWT.
This enables the RP to authenticate against the SIOP using the
RP's DID. The Request Object can be passed by value in the
request request parameter, or by reference using the request_uri parameter.
The Request Object follows the OIDC specification, e.g., adding nonce,
state, response_type, and client_id parameters.
This specification introduces additional rules for request parameters and claims in the Request Object:
-
REQUIRED.
issMUST contain the DID of the RP that can be resolved to a DID Document. The DID Document MUST contain a verification method in the authentication section, e.g., public key, that allows the SIOP to verify the Request Object. -
REQUIRED.
kidMUST be a DID URL referring to a verification method in the authentication section in the RP's DID Document, e.g.,did:example:0xab#key1. The SIOP MUST be able to use that verification method to verify the Request Object directly or indirectly. Additionally, the referred JWKS in theregistrationparameter MUST contain an entry with the samekid. -
REQUIRED.
scopeMUST includedid_authnto indicate the SIOP DID profile is used. -
REQUIRED.
registrationMUST be included in the Request Object -
REQUIRED.
client_idMUST be repeated in the Request Object -
OPTIONAL.
response_modespecifies how the response is returned to the redirect URI by the SIOP. SIOP implementing this specification MAY set theresponse_modetoform_post.fragmentis the default Response Mode. RPs MUST take into consideration the platform of the User-Agent when specifying this request parameter. -
OPTIONAL.
response_contextspecifies whether the response should be returned to the redirect URI in the context of an existing system browser session, or whether the response can be returned in a new/empty context (requested with aresponse_contextofwallet). The defaultresponse_contextisrp, indicating that the response should be submitted in the conext of the RP's existing system browser session. -
OPTIONAL.
claimsfollows the OIDC Core schema, adding a top-levelvcproperty as a sibling to (and following the schema of)id_tokenanduserinfo. Requesting claims within thevcset indicates that the requesting party would like to receive (ifessentialisfalse), or requires (iftrue) a specific set of verifiable credential types within the.vp.verifiableCredentialarray of the SIOP Response. Specific [VC types](https://www.w3.org/TR/vc-data-model/#types) are identified using the VC type's full URI.
By default, the iss claim refers to the client_id but SIOP
assumes that client_id is the redirect URI of the RP. That is the reason
why the DID is not encoded in the client_id. It is compliant with the
OIDC specification to use different values for iss and
client_id.
See OAuth 2.0 Form Post Response Mode [[?OAuth2.FormPost]] and OAuth 2.0 Multiple Response Type Encoding
Practices [[?OAuth2.ResponseTypes]] for more information about response_mode.
A response_context of wallet indicates to the SIOP that the user flow should end in the SIOP,
without any in-band redirection back to the RP. This behavior is useful in cross-device workflows where
it's appropriate for the mobile portion of the flow to terminate in the wallet.
When providing claims in this manner, the SIOP Response acts as a W3C Verifiable Presentation; requested claims are provided in the Response by populating the array of Verifiable Credentials within the Presentation.
The following is a non-normative example of the JWT header of a Request Object:
{
"alg": "ES256K",
"typ": "JWT",
"kid": "did:example:0xab#veri-key1"
}
The following is a non-normative example of the JWT payload of a Request Object without requesting
<SIOP DID Response> encryption:
{
"iss": "did:example:0xab",
"response_type": "id_token",
"client_id": "https://my.rp.com/cb",
"scope": "openid did_authn",
"state": "af0ifjsldkj",
"nonce": "n-0S6_WzA2Mj",
"response_mode" : "form_post",
"registration" : {
"jwks_uri" : "https://uniresolver.io/1.0/identifiers/did:example:0xab;transform-keys=jwks",
"id_token_signed_response_alg" : "ES256K"
}
}
The following is a non-normative example HTTP 302 redirect response by the RP, which triggers the User-Agent to make an SIOP DID Authentication Request using Request Object by value to the SIOP (with line wraps within values for display purposes only):
HTTP/1.1 302 Found
Location: openid://?
&client_id=https%3A%2F%2Frp.example.com%2Fcb
&scope=openid%20did_authn
&request=<JWT>
The following is a non-normative example HTTP 302 redirect response by the RP, which triggers the User-Agent to make an SIOP DID Authentication Request using Request Object by reference to the SIOP (with line wraps within values for display purposes only):
HTTP/1.1 302 Found
Location: openid://?
response_type=id_token
&client_id=https%3A%2F%2Frp.example.com%2Fcb
&scope=openid%20did_authn
&request_uri=https%3A%2F%2Frp.example.com%2F90ce0b8a-a910-4dd0
Encryption
JWE encryption SHOULD use Diffie-Hellman key agreement, i.e., algorithm `ECDH-ES` using the `X25519` curve which uses direct key agreement with an ephemeral key. This means that a symmetric key is derived using Diffie-Hellman from the RP's public key and a randomly generated ephemeral private key. The corresponding ephemeral public key is included in the header of the JWE in the `epk` and the derived symmetric key is used to directly encrypt the JWT content. For symmetrically encrypting the content `XChaCha20Poly1305` is used which has algorithm code `XC20P`.
The following is an example of the protected header of the resulting JWE:
{
"alg": "ECDH-ES",
"epk":
{
"kty": "OKP",
"crv":"X25519",
"x":"hSDwCYkwp1R0i33ctD73Wg2_Og0mOBr066SpjqqbTmo"
}
"enc": "XC20P",
"kid": "did:example:0xab#key-1"
}
Note that the `kid` above denotes the DID and key of the RP, i.e., this public key is the key used by the sender together with the ephemeral private key in order to derive the shared secret. For the encryption the 24 bytes nonce field in the `XChaCha20` algorithm is used as the initialization vector. The authentication tag is the MAC computed by the `Poly1305` function. It is 16 bytes long.
The message to be encrypted is the JWT of the `id_token`, including header and signature. The JWT is encoded via base64url before encryption.
For the final encoding of the JWE the JWE Compact Serialization outlined in [[!RFC7516]] is used. The structure of the message is as follows:
BASE64URL(JWE Protected Header) || '.' || '.' ||
BASE64URL(JWE Initialization Vector) || '.' ||
BASE64URL(JWE Ciphertext) || '.' ||
BASE64URL(JWE Authentication Tag)
Note the two '.' characters above which indicates that the encrypted key is empty since we are using direct key agreement.
SIOP Request Validation
The SIOP MUST validate the <SIOP Request> by following the
Self-Issued ID Token Validation rules as per [[!OIDC.Core]].
The step described above ensures that the Request Object is verified according to the OIDC specification. This includes basic JWS verification.
If scope contains the did_authn scope, the receiving SIOP
MUST further validate the <SIOP Request> as follows in no particular order:
-
Resolve the DID Document from the
RP's DID specified in the
issrequest parameter. -
If
jwks_uriis present, ensure that the DID in thejwks_urimatches the DID in theissclaim. -
Determine the verification method from the RP's
DID Document that matches the
kidof theSIOP Request. -
Verify the
SIOP Requestaccording to the verification method above. This step depends on the verification method in the authentication section in the DID Document and is out-of-scope of this specification.
If the key pair that signed the SIOP Request refers to the same key as indicated by the
verification method, then no additional verification has to be done as the SIOP
validation will verify the signature of the JWS.
Generate SIOP Response
The SIOP MUST generate and send the <SIOP Response> to the
RP as described in the Self-Issued OpenID Provider Response section in [[!OIDC.Core]].
The id_token represents the <SIOP Response> encoded as a JWS, or nested JWS/JWE.
This specification introduces additional rules for claims in the id_token:
-
REQUIRED.
sub_jwkMUST contain akidthat is a DID URL referring to the verification method in the SIOP's DID Document that can be used to verify the JWS of theid_tokendirectly or indirectly. -
REQUIRED.
didMUST be the SIOP's DID.
The sub_jwk claim has to be provided for backward compatibility reasons. The verification
method in the DID Document can be different from a public key and can use a
publicKey property value other than publicKeyJwk.
The following is a non-normative example of the JWT header of an id_token using no encryption:
{
"alg": "ES256K",
"typ": "JWT",
"kid": "did:example:0xab#key-1"
}
The following is a non-normative example of the unencrypted JWT payload of an id_token:
{
"iss": "https://self-issued.me",
"nonce": "n-0S6_WzA2Mj",
"exp": 1311281970,
"iat": 1311280970,
"sub_jwk" : {
"crv":"secp256k1",
"kid":"did:example:0xcd#verikey-1",
"kty":"EC",
"x":"7KEKZa5xJPh7WVqHJyUpb2MgEe3nA8Rk7eUlXsmBl-M",
"y":"3zIgl_ml4RhapyEm5J7lvU-4f5jiBvZr4KgxUjEhl9o"
},
"sub": "9-aYUQ7mgL2SWQ_LNTeVN2rtw7xFP-3Y2EO9WV22cF0",
"did": "did:example:0xcd"
}
SIOP Response Validation
The RP MUST validate the <SIOP Response> as described in the
Self-Issued ID Token Validation section in [[!OIDC.Core]]. This includes:
-
Optionally decrypting the JWE to obtain the JWS which contains the
id_token. -
Verifying that the
id_tokenwas signed by the key specified in thesub_jwkclaim.
Additionally, the RP MUST validate the id_token against the
SIOP's DID Document as follows:
-
Resolve the DID Document from the
SIOP's DID specified in the
didclaim. -
Determine the verification method from the SIOP's DID
Document that matches the
kidof thesub_jwkclaim in theid_token. -
Verify the
id_tokenaccording to the verification method above. This step depends on the verification method in the authentication section in the DID Document and is out-of-scope of this specification.
If the key pair that signed the id_token refers to the same key as indicated by the
verification method, then no additional verification has to be done as the SIOP
validation will verify the signature of the JWS.
SIOP Discovery
The SIOP specification assumes the following OP discovery metadata:
"id_token_signing_alg_values_supported": ["RS256"],
"request_object_signing_alg_values_supported": ["none", "RS256"]
The DID AuthN profile assumes the following OP discovery metadata:
"id_token_signing_alg_values_supported": ["RS256", "ES256K", "EdDSA"],
"request_object_signing_alg_values_supported":
["none", "RS256", "ES256K", "EdDSA"]
This change will allow DID AuthN enabled RPs to use additional signature algorithms commonly used amongst members of the SSI community.
"Self-Issued OpenID Provider Discovery" IS NOT normative and does not contain any MUST, SHOULD, or MAY
statements. Therefore, using a different signing algorithmn than RS256 shouldn't break the
SIOP specification. A DID AuthN enabled RP
would provide id_token_signed_response_alg to indicate its preferred signature algorithm
among the three id_token_signing_alg_values_supported options listed above.