keri
Key Event Receipt Infrastructure - the spec and implementation of the KERI protocol
Glossary
Definitions
Abbreviations
In alphabetic order:
AID = Autonomic Identifier
AIS = Autonomic Identity System
AN = Autonomic Namespace
DID = Decentralized Identity or Digital Identity dependent of the context.
DIF = Decentralized Identity Foundation
DHT = Distributed Hash Table
DKMI = Decentralized Key Mangement Infrastructure
KAACE = KERI Agreement Algorithm for Control Establishment
KEL = Key Event Log
KERL = Key Event Receipt Log
KERI = Key Event Receipt Infrastructure
LOA = Levels Of Assurance
PKI = Public Key Infrastructure
SAI = Self Addressing Identifier
SCI = Self Certifying Identifier
SSI = Self Sovereign Identity
VC = Verifiable Credential, look up W3D DID standardization for more info
WASM = WebAssembly
Definitions in alphabetic order:
Ambient verifiability
Verifiable by anyone, anywhere, at anytime. E.g. Ambient Duplicity Detection describes the possibility of detecting duplicity by anyone, anywhere, anytime.
Agent
A representative for an identity. MAY require the use of a_wallet_. MAY support transfer
Agency
Agents can be people, edge computers and the functionality within wallets. The service an agent offers is agency.
Autonomic Identifier
An identifier that is self-certifying and self-sovereign
Autonomic Namespace
A namespace that is self-certifying and hence self-administrating. ANs are therefore portable = truly self sovereign.
Autonomic idenity system
In the design of an identity system you need to answer a few questions.
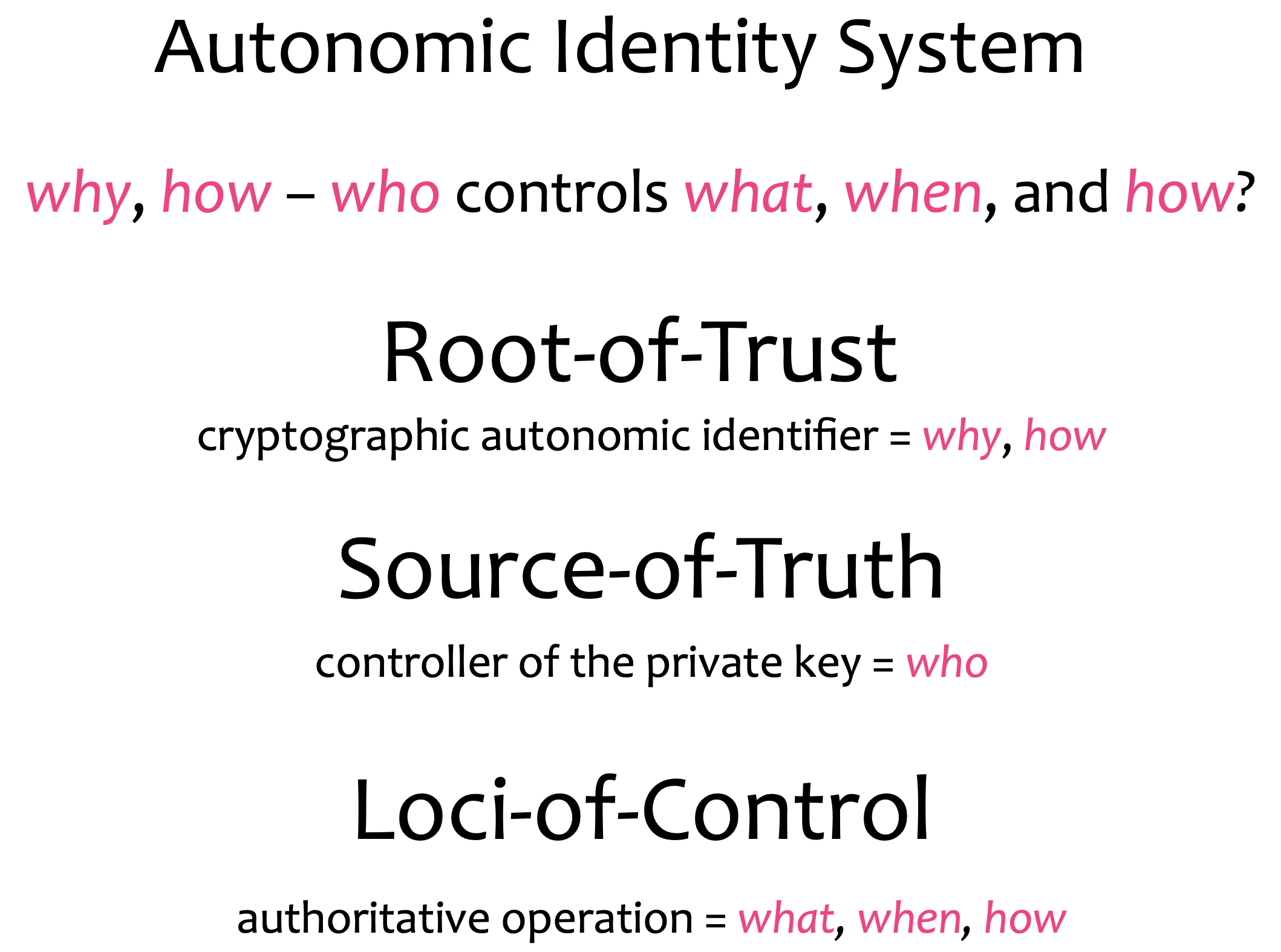
There’s nobody that can intervene with the establishment of the authenticity of a control operation because you can verify all the way back to the root-of-trust.
Claim
An assertion of the truth of something, typically one which is disputed or in doubt. A set of claims might convey personally identifying information: ½name, address, date of birth and citizenship, for example. (Source).
Content-addressable hash
Content addressing is a way to find data in a network using its content rather than its location. The way we do is by taking the content of the content and hashing it. Try uploading an image to IPFS and get the hash using the below button. In the IPFS ecosystem, this hash is called Content Identifier, or CID.
Controller
The entity that has the ability to make changes to an identity, cryptocurrency or v_erifiable credential_.
The controller of an autonomous identifier is the entity (person, organization, or autonomous software) that has the capability, as defined by derivation, to make changes to an Event Log. This capability is typically asserted by the control of a single inception key. In DIDs this is typically asserted by the control of set of cryptographic keys used by software acting on behalf of the controller, though it may also be asserted via other mechanisms. In KERI an AID has one single controller. Note that a DID may have more than one controller, and the DID subject can be the DID controller, or one of them.
Correlation
An identifier used to indicate that external parties have observed how wallet contents are related. For example, when a public key is reused, it conveys that some common entity is controlling both identifiers. Tracking correlation allows for software to warn when some new information might be about to be exposed, for example: “Looks like you are about to send crypo currency, from an account you frequently use to a new account you just created.”
Cryptocurrency
A digital asset designed to work as a medium of exchange wherein individual coin ownership records are stored in a digital ledger or computerized database using strong cryptography to secure transaction record entries, to control the creation of additional digital coin records. See more
Decentralized Identity
DID; Decentralized identity is a technology that uses cryptography to allow individuals to create and control their own unique identifiers. They can use these identifiers to obtain Verifiable Credentials from trusted organisations and, subsequently, present elements of these credentials as proof of claims about themselves. In this model, the individual takes ownership of their own identity and need not cede control to centralized service providers or companies.
KERIs definition of decentralization (centralization) is about control not spatial distribution. In our definition decentralized is not necessarily the same as distributed. By distributed we mean that activity happens at more than one site. Thus decentralization is about control and distribution is about place. To elaborate, when we refer to decentralized infrastructure we mean infrastructure under decentralized (centralized) control no matter its spatial distribution. Thus decentralized infrastructure is infrastructure sourced or controlled by more than one entity.
Derivation code
{TBW}
Duplicity
In KERI consistency is is used to described data that is internally consistent and cryptographically verifiably so. Duplicity is used to describe external inconsistency. Publication of two or more versions of a KEL log, each of which is internally consistent is duplicity. Given that signatures are non-repudiable any duplicity is detectable and provable given possession of any two mutually inconsistent versions of a KEL.
Entropy
Unpredictable information. Often used as a secret or as input to a key generation algorithm.More
Establishment Event
{TBW}
End verifiable log
End verifiable logs on ambient infrastructure enables ambient verifiability (verifiable by anyone, anywhere, at anytime). We don’t need the intermediate states of the log.
Entity
Entities are not limited to natural persons but may include groups, organizations, software agents, things, and even data items.
Event sourced architecture
It is an Event driven architecture. However in Event Driven you can’t ever replay an event.
In the Event Sourced architecture you recreate states in an asynchronous way. That has in general great scaleability and resiliance characteristics. However, in KERI the driver for event sourcing is security.
External consistency
Two or more logs are externally consistent if they are both verfiable internally consistent, to begin with, and the reported copies of the logs that are the same.
External logs that are inconsitent, have at least two reported copies of the logs that are different. That means I have a duplicitous log. We need duplicity detection to be able to garantuee external consistency or put in an different way: duplicity detection protects against external inconsistency.
Inception Event
{TBW}
Inconsistency
{TBW}
Identity
A unique entity. Typically represented with a unique identifier.
Internal inconsistency
In KERI we are protected against Internal inconsistency by the hash chain datastructure of the KEL, because the only authority that can sign the log is the controller itself.
KERI Agreement Algorithm for Control Establishment
{TBW}
Keridemlia
It is a contraction of KERI and Kademlia. It’s the distributed database of Witness IP-addresses based on a Distributed Hash Tabel. It also does the CNAME - stuff that DNS offers for KERI: the mapping between an identifier and it’s controller AID stored in the KEL to its current wittness AID and the wittness AID to the IP address.
(@henkvancann)
Key
A mechanism for granting or restricing access to something. MAY be used to issue and prove, MAY be used to transfer and control over identity and cryptocurrency. More
Key Event Log
{TBW}
Key Event Receipt Log
{TBW}
Key Event State
Includes the mapping CNAME like, it also contain the witness data
The KES is never signed by the controller of the AID
{TBW}
Level of Assurance
LOA; Identity and other trust decisions are often not binary. They are judgement calls. Any time that judgement is not a simple “Yes/No” answer, you have the option for levels of assurance. KERI has the same LOAs for entropy and trust in human behaviour preservering the security of keypairs and preservering their own privacy. It has high LOAs for the cryptographical bindings of controllers and identifiers. Also the validation of witnesses and watchtowers has high a LOA.
Non-Establishment Event
{TBW}
Normative
In general, we call a theory “normative” if it, in some sense, tells you what you should do - what action you should take. If it includes a usable procedure for determining the optimal action in a given scenario. Souce.
Non-normative
A theory is called non-normative if it does not do that. In general, the purpose of non-normative theories is not to give answers, but rather to describe possibilities or predict what might happen as a result of certain actions. Souce.
Payload
The term ‘payload’ is used to distinguish between the ‘interesting’ information in a chunk of data or similar, and the overhead to support it. It is borrowed from transportation, where it refers to the part of the load that ‘pays’: for example, a tanker truck may carry 20 tons of oil, but the fully loaded vehicle weighs much more than that - there’s the vehicle itself, the driver, fuel, the tank, etc. It costs money to move all these, but the customer only cares about (and pays for) the oil, hence, ‘pay-load’. source.
Now payload in KERI. The payload of an item in an Event Log is one the following cryptographical building blocks in KERI:
- a content digest hash
- a root hash of a Merkletree
- a public key
Note that the KERI never puts raw data or privacy sensitive data in a
KELorKERL.
Public Key Infrastructure
A public key infrastructure (PKI) is a set of roles, policies, hardware, software and procedures needed to create, manage, distribute, use, store and revoke digital certificates and manage public-key encryption. [Wikipedia].(https://en.wikipedia.org/wiki/Public_key_infrastructure)
Race condition
A race condition or race hazard is the condition of an electronics, software, or other system where the system’s substantive behavior is dependent on the sequence or timing of other uncontrollable events. It becomes a bug when one or more of the possible behaviors is undesirable. Source.
Root of trust
Replace human basis-of-trust with cryptographic root-of-trust. With verifiable digital signatures from asymmetric key cryptography we may not trust in “what” was said, but we may trust in “who” said it.
The root-of-trust is consistent attribution via verifiable integral non-repudiable statements.
Seal
A seal is a cryptographic anchor that provides evidence of authenticity; we have:
- Digist Event Seal
- Hash tree root Seal
- Event Seal Seals deliver authenticity proofs in KERI.
Secret
Information controlled by an identity. MAY be used to derive _key_s.
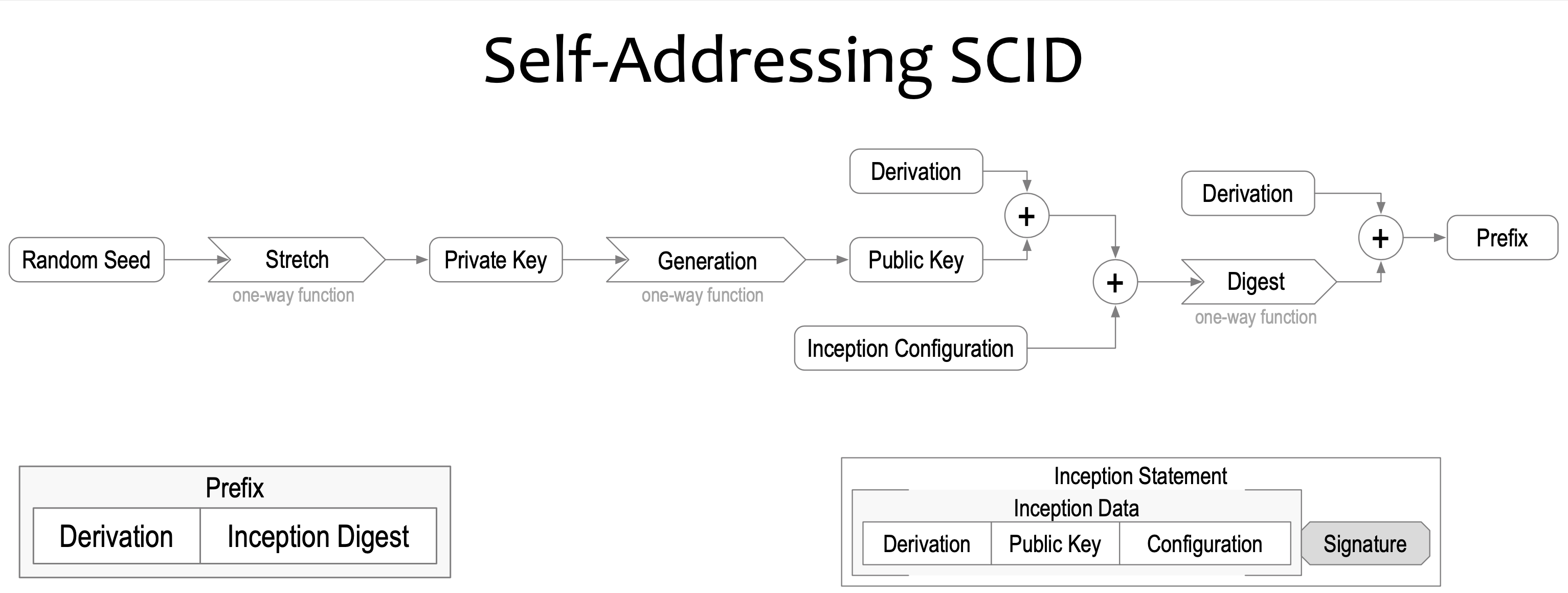
Self Addressing Identifier
SAI, This is a self certfifying identifier (SCI) that has been attached to a certain context or infrastructure at the time of its inception. The inception configuration together with public key and it’s derivation, forms a digest (hash) plus it’s own derivation code that constitutes the Prefix of a self-addressing ID.
Self Certifying Identifier
A controller of issues an own Identifier by binding a generated public private keypair to an identifier. After this a controller is able to sign the identifier and create a certificate.
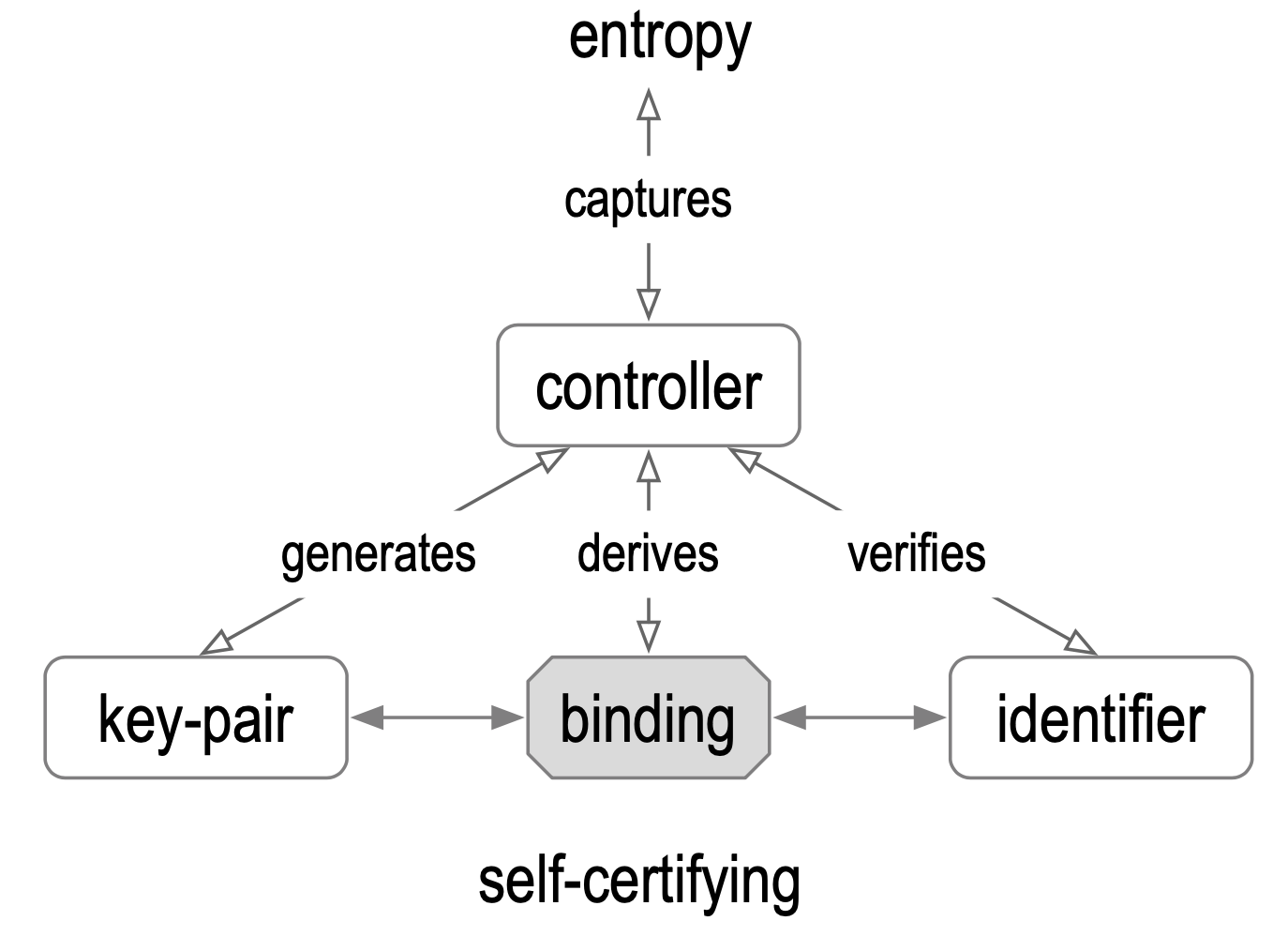
The root-of-trust is fully cryptographic, there is no infrastructure associated with it. If we start there we can build a secure system on top of that. It means SCI gives us strong bindings between the keypair, the controller and the identifier. And so it fixes the main weakness of any administratively issued identifier asserting the binding between the keypair and the identifier and between the controller and the identifier, replacing them with all cryptographically strong bindings.
Self Sovereign Identity
SSI is a new model for Internet-scale digital identity based on an emerging set of protocols, cutting edge cryptography and open standards. Technological and social movements have come together that make SSI possible.
Source.
Decentralisation of the root-of-trust and verifiable credentials come into play and delivers “user-centric identity”: more control and self-determination of individuals, individuals machines and combinations of these, that identify as one.
(@henkvancann)
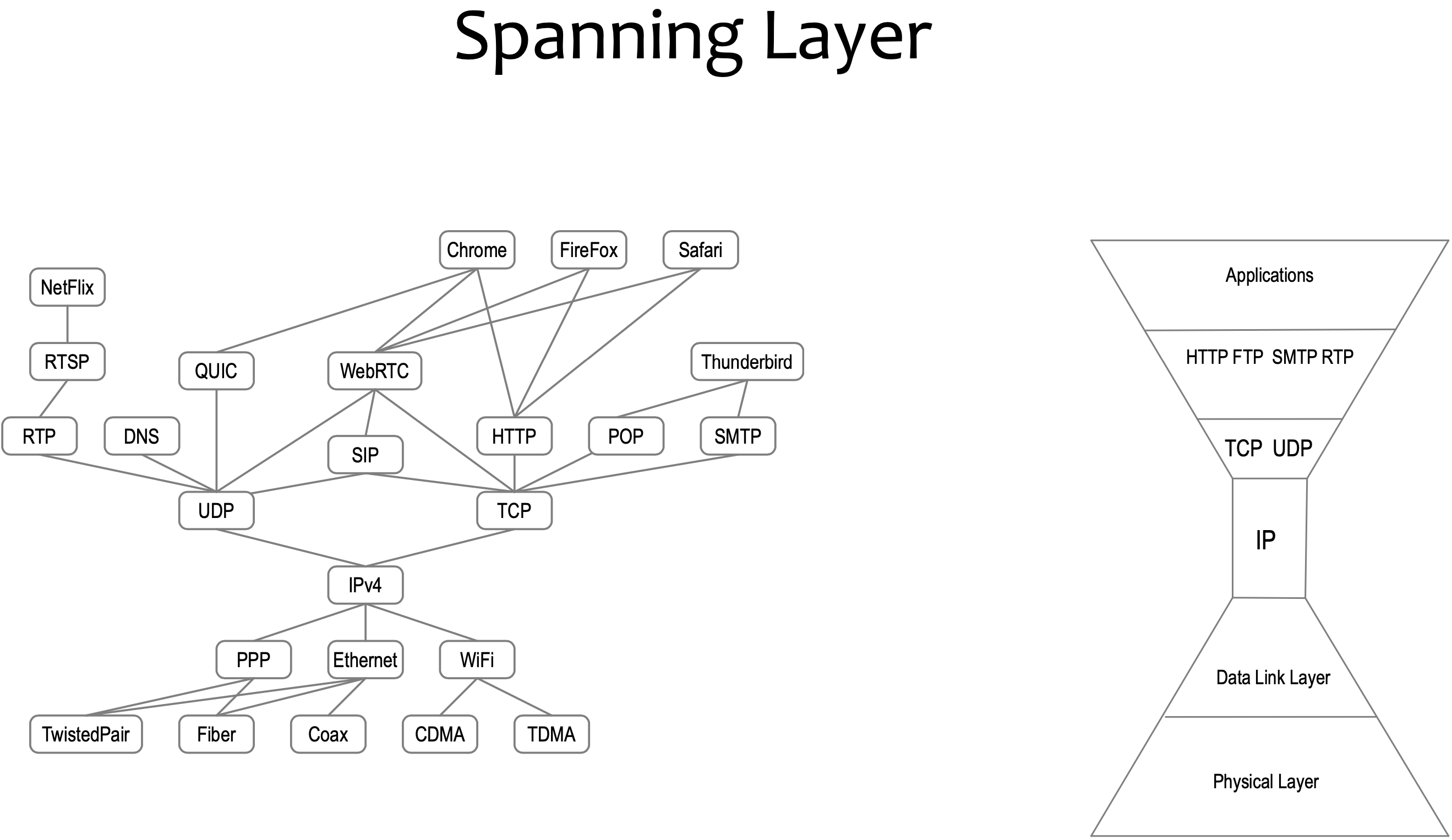
Spanning layer
An all encompassing layer horizontal layer in a software architecture. Each trust layer only spans platform specific applications. It bifurcates the internet trust map. There is no spanning trust layer.
Subject
A digital subject: A person or thing represented or existing in the digital realm which is being described or dealt with. (Source).
Transfer
The process of changing the controller of cryptocurrency, identity or verifiable credential. MAY require the use of a key.
Trust-over-IP
It’s a term related to the effort of a foundation. The Trust over IP Foundation is an independent project hosted at Linux Foundation to enable the trustworthy exchange and verification of data between any two parties on the Internet. More.
Validator
a validator is anybody that wants to estblish control-authority over an identifier, created by the controller of the identifier. Validators verify the log, they apply duplicity detection or they leverage somebody else’s duplicity detection or apply any other logic so they can say “Yes these are events I can trust”.
During validation of virtual credentials for example, a verifier checks to see if a verifiable credential (VC) has been signed by the controller of this VC using the applicable verification method.
Verifiable Credential
VC; A data model for conveying claims made by an issuer about a subject. See vc-data-model for more.
W3C DID
The W3C consortium Decentralized ID standardization. More.
WebAssembly
WASM, or just WA) is an open standard that defines a portable binary-code format for executable programs, and a corresponding textual assembly language, as well as interfaces for facilitating interactions between such programs and their host environment.
The main goal of WebAssembly is to enable high-performance applications on web pages, but the format is designed to be executed and integrated in other environments as well, including standalone ones. More info.
(Digital Identity) Wallet
In our context it is software and sometimes hardware that serves as a key store and functionality. Keys can be private keys and public keys, hashes and pointers. Functionality can be signing, invoices (receive), send, virtual credentials, delegation, etc. This is the agency part of a wallet.
More about digital ID Wallets
More about cryto Wallets.